The 2011 Arab Spring unrests were a pivotal moment in the history of protests. New use of social media and digital technologies allowed citizens to organize mass demonstrations, spreading the wave of dissent even across borders. At the same time, it was also the first time the internet went dark.
Now, 11 years later, internet shutdowns and social media blocks have become common practice among worldwide governments as a means to silence protesters and hide rights abuses.
However, citizens around the world have learned to fight back. And, the answer always lies in digital technology. That’s how security and circumvention software like the best VPN services have become the everyman’s favorite weapon in times of conflict.
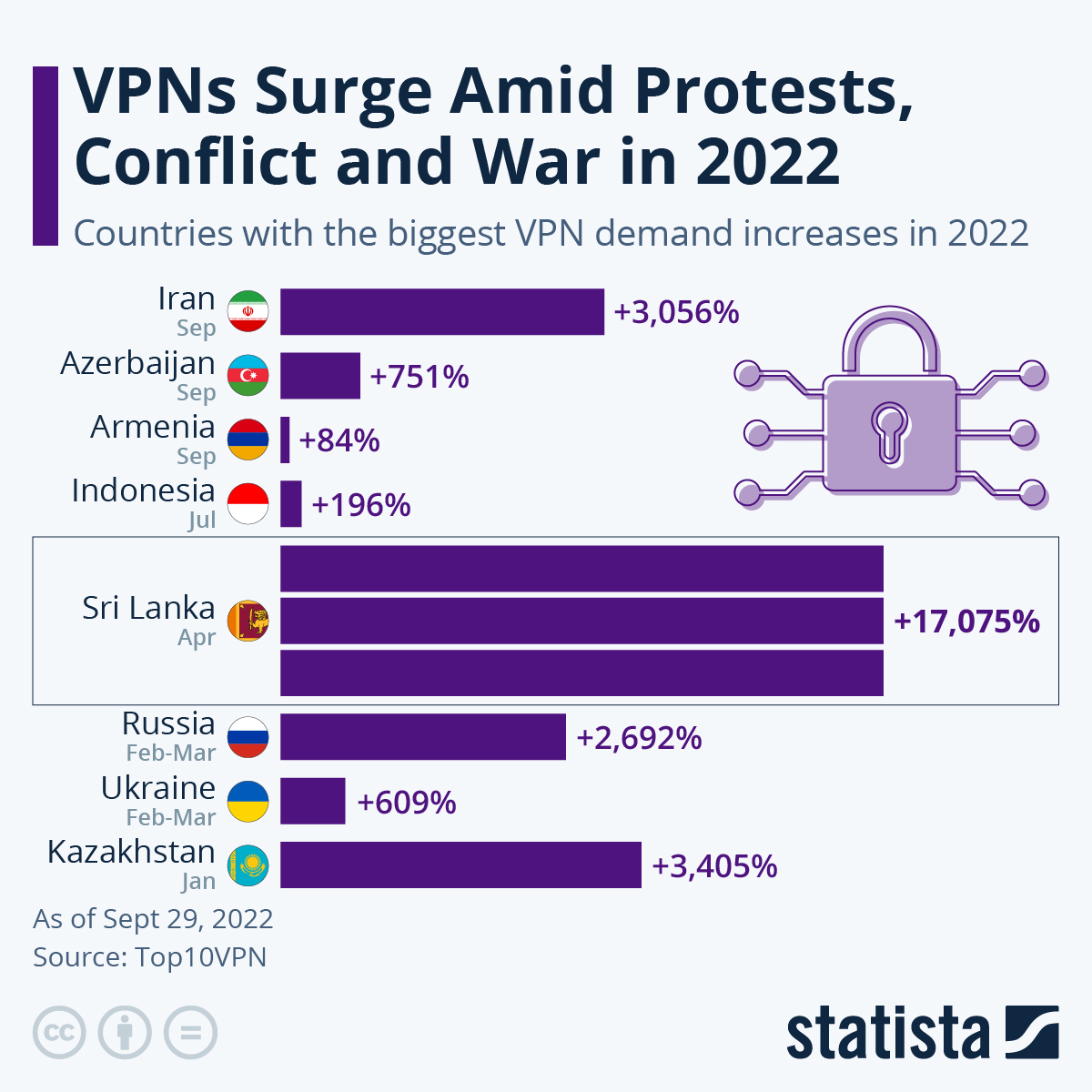
We recently saw how VPN demand rose among Iranians after authorities restricted Instagram and WhatsApp to clamp down on the ongoing rallies over the death of 22 year-old Mahsa Amini at the hands of Iranian morality police. VPN downloads soared more than 3,000%.
However, 2022 has been witnessing a surge in VPN downloads around the globe since January – perhaps as never before. Below we’ve got a breakdown of the most important events.
2022 at a glance
We’ve had some pretty busy months lately in terms of internet shutdowns, online censorship and cyberattacks. All this pushed people around the world to turn to secure VPN services to bypass internet restrictions and protect their digital privacy.
The year kicked off with over 460% more downloads in Myanmar where the block of Facebook made the circumvention tool a necessity for Burmese citizens. What’s more, this rise in demand occurred despite the country’s digital dictatorship seeking to criminalize VPNs.
This was nothing in comparison with the leap registered in Kazakhstan, though. Following disruptions of mobile internet access amid anti-government protests, the rise in VPN demand skyrocketed around 3,400% on January 5.
Another staggering increase came from Sri Lanka in April, with a peak of more than 17,000%. This prompted the government to lift social media bans as VPNs make it “completely useless.”
Between February and March there was the beginning of the conflict in Ukraine to shake people’s digital balance. So that fierce online censorship, together with a rise in cybercrime, has brought VPN demand to a new high in the region.
Russia VPN downloads kept soaring, reaching a peak of nearly 2,700%. That’s not surprising as the Kremlin boosted its internet restrictions even further, blocking many national and foreign news sites along the way.
In Ukraine the demand has seen more than a 600% increase since the war started. Many providers even offered free subscriptions to support journalists working in the country.
In Indonesia there was a surge of 196% in July following new internet regulations that blocked many platforms, like PayPal and Twitter, for failing to comply with new rules.
The same month, VPN downloads soared in Cuba to bypass internet disruptions enforced to crack down on citizens filling the street to protest against a staggering economic crisis. Over 34,000 more Psiphon downloads were recorded.
More recently, a military conflict erupted on the border between Azerbaijan and Armenia, causing a rise of security software across the region. People in Azerbaijan have been downloading VPN services 750% more since the clashes started on September 14. While, in Armenia, the VPN demand was 84% higher than in August.

How a VPN can help
Short for virtual private network, a VPN is a security software that spoofs your IP address location while securing your data inside an encrypted VPN tunnel.
While VPNs are ineffective in case of a complete internet blackout, they are the perfect tool for accessing blocked social media platforms, apps and sites.
During times of conflict, cybercrime is also likely to rise. Authorities might boost their online surveillance to crack down on dissidents, too. Reliable VPN services are then vital for browsing the web anonymously and preventing nosy governments and malicious actors from accessing your data.
It’s worth noting that authoritarian governments might block VPN usage. This is why it’s important to opt for a service integrated with obfuscation technology to evade these blocks. Other features you should look out for include a strict no-logs policy, strong encryption protocols and additional security options like kill switch and split tunneling.